This post will guide you how to use Kusto query to classify the log data based on some log is just contain a string, and you want to separate the string into different column for easy view.
The steps for the whole configuration will be:
- Create a new Workbook
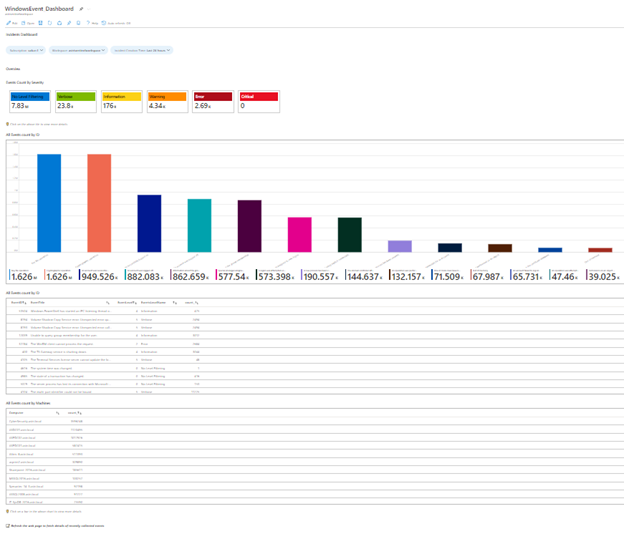
- Develop a customized Workbook for Windows Server
- Log Data Classification
Step 1 – Create a new Workbook
Visit to “Sentinel” and select “Workbook”, then click “Add workbook” to create a blank workbook.
Step 2 – Develop a customized Workbook for Windows Server
For the Sentinel Workbook, you can make the dashboard like our example.
For Workbook Design detail information, please visit our post:
Azure Sentinel – A Guide for Customizing Sentinel Workbook (Kusto Query) for Sentinel Incidents
Step 3 – Log Data Classification
This is the primary KQL for the log data classification for Windows Server Event Message:
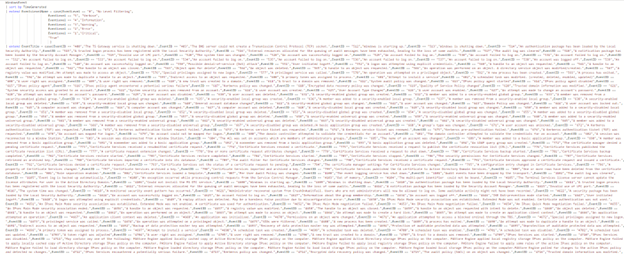
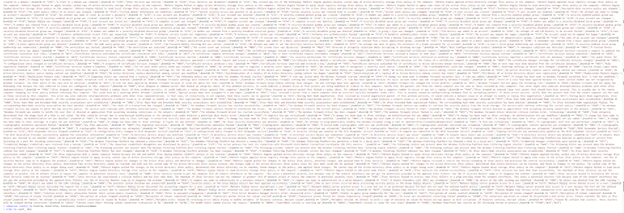
Based on Windows Event Log do not have raw data about Event Name, so we have exported all the Event log Name into a CSV, and use looping to construct the KQL for column “EventTitle”
For the above example, you need to extend the custom column and use some string operation for doing the log data classification.
You can visit our SOS GitHub for downloading the source code as a template:
https://github.com/SOSHKMVP/AzureSentinel-Workbook/blob/main/WindowsEvents_Dashboard.txt

Eric Chan
Microsoft MVP
SOS Group Limited

